What is DNS hijacking? DNS hijacking explained
This post was sponsored by AT&T Business, but the opinions are my own and don’t necessarily represent positions or strategies of AT&T Business.
DNS hijacking, also known as DNS redirection, has been used to successfully victimize websites globally ranging from Fortune 100 companies to small mom and pop stores.
DNS hijacking redirects web traffic from the intended destination to a new, malicious source. Often, the victim will not even be aware they were redirected since their URL will appear the same in their browser. While DNS hijacking continues to be a threat, there are many ways and services to mitigate and protect a DNS for your employees and users.
This article explores what is DNS hijacking in more detail, explain how it works, and demonstrates how to prevent DNS hijacking so businesses can avoid falling victim to the attack.
What is DNS hijacking?
DNS (Domain Name System) is the protocol that translates the URL in your search bar to an IP address that a computer can understand. Whenever you search for a URL, it will send a query to a DNS resolver, which tracks down and converts the IP address for a host name, to locate the IP address and direct you to the site. Think of DNS as the internet’s address book.
DNS hijacking works by causing the DNS query to be incorrectly resolved. Instead of being sent to the intended site, the query will direct you to a different — and typically malicious — one.
For attackers, there are numerous motivations for launching a DNS hijacking attack, such as:
- Disrupting a site and causing lost money and reputational damage
- Posing as a trustworthy site to collect user information (phishing)
- Espionage, that is, spying on your company’s network activities
How DNS hijacking works
There are several different ways DNS hijacking can work. Some of the most common methods include:
- “Man-in-the-middle” attacks where attackers (sitting “in the middle” of the server and requester) intercept a DNS request to a server and redirect it to another compromised server by providing a different IP address
- Infecting a user’s machine with malware and using it to change settings and redirect DNS requests to the attacker’s server. Since the URL in the user’s browser remains the same, it’s difficult for users to notice these attacks.
- Attacking a router and changing the DNS settings. This severe attack affects all users connected to that router and is often easily accomplished by taking advantage of weak passwords and other common vulnerabilities.
- Attacking the DNS server directly and changing the records, redirecting any DNS requests to a new site
DNS hijacking explained: How to prevent DNS hijacking
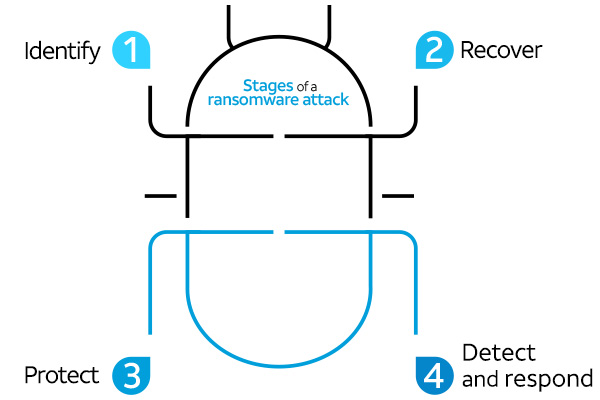
DNS hijacking is often successful simply because many organizations either don’t know how to detect DNS hijacking or simply fail to take enough precaution. As a result, many neglect to monitor their DNS traffic for malicious activity. The good news is that by taking some precautions, you can take measures to mitigate the risks of DNS hijacking. Here are four steps you need to keep in mind:
1. Use a firewall to protect real resolvers
The DNS resolver sends queries to and from the DNS. A fake resolver can be used in DNS hijacking, redirecting traffic to a phony website. For this reason, it’s crucial to ensure your legitimate resolvers are always safely behind a firewall — blocking access to anyone outside the organization.
Resolvers should always be carefully monitored, and you should shut down any unneeded ones quickly.
2. Educate staff on security best practices
Everyone working in your organization should be aware of what to do (and what not to do) to know how to prevent DNS hijacking.
Thankfully, most of these best practices are in line with standard cybersecurity measures for good hygiene.
- Avoid clicking on questionable links or links within emails from outside the organization
- If unsure of an email, always verify
- Don’t use public Wi-Fi networks to share sensitive information or login credentials
- Pay attention to any suspicious details in URLs (they should have a valid SSL certificate)
- Use a reliable virtual private network (VPN)
- Embrace a robust password management policy that promotes strong passwords, frequent password changes, or both
3. Restrict access to name servers
A name server is a server where your DNS information is stored, and it’s essential to keep these servers as protected as possible. Use physical security, multi-factor authentication, and a strong firewall to prevent malicious actors from gaining access. It’s also important to separate the authoritative name server from the resolver ensures that an attack on one server won’t impact the other.
4. Immediately patch known vulnerabilities
Hackers are always on the lookout for the low-hanging fruit of vulnerable DNS servers. By taking simple steps, you’ll deter and defend against these attacks. A good patch management program within your organization is strongly recommended.
How AT&T Cybersecurity Services can help
AT&T Business has many solutions to mitigate the threat of DNS hijacking. Whether the attacks install malware, take over routers, or intercept DNS communication, we can help your organization defend against them.
Solutions like Network Security Services and Enterprise Traffic Protector can defend against DNS hijacking from multiple angles, giving your organization peace of mind and security in today’s evolving threat landscape.
Other helpful reading from AT&T Business about how to keep your business cybersecure:
- What is a VPN and how does it work?
- How DNS filtering can help protect your business from cybersecurity threats
- Software-Defined Networking (SDN) and its security benefits
Learn more about AT&T Cybersecurity Solutions or contact your representative for more information.



Share
Share this with others