Cybersecurity as a Service (CSaaS) explained
With the changing cybersecurity landscape, it’s hard for even large enterprises to keep up with the volume, velocity, and variety of threats. And, as companies pivot to network modernization, understanding cybersecurity controls and which ones are most beneficial to your business is an important step to protect your data and ultimately your business.
This article will discuss Cybersecurity as a Service (CSaaS) as an option for businesses, small to large. We’ll use Zero Trust and secure access service edge (SASE) as a use case. We’ll define what a Zero Trust environment is and how a managed security services provider (MSSP) may get you there sooner.
We’ll explore how SASE can help as well, because while the market may conflate Zero Trust and SASE, they’re not one and the same. Implementing Zero Trust and SASE may be confusing, hence an MSSP and consulting services can help expedite the process that can effectively protect your business.
[Read: What is SASE?]
What is CSaaS?
CSaaS is a pay-as-you-go approach to cybersecurity. As with all SaaS offerings, it’s a subscription model with a third-party vendor. Services offered vary and can be tailored to your needs. These can include threat monitoring, compliance with industry standards, employee training, and penetration testing, which simulates an attack on your network.
A key focus of these services is preventing malware, such as ransomware, from impacting your business.
With cybersecurity skills difficult to hire for today, CSaaS can be an attractive option because it takes the burden off of the business to maintain a cybersecurity team. In addition, it allows you to scale as your business grows.
This means you won’t need to keep recruiting and hiring cybersecurity professionals – a big bonus in this competitive environment. Expertise in things such as SASE and Zero Trust is hard to find. Sometimes it just makes more financial sense and can improve an organization’s risk posture by working with a trusted third-party advisor.
Core components of CSaaS
Modern CSaaS offerings are far more than simple threat monitoring tools. They’ve advanced to include multi-layered security to provide better protection against the ever-evolving threat landscape. In these layers there are multiple components, which include:
Threat monitoring and incident response
CSaaS ensures real-time monitoring of your network, detecting anomalies and addressing potential vulnerabilities before they escalate. In the event of a breach, immediate incident response measures minimize downtime and secure critical systems.
You can also run tests and simulations to identify additional weak spots so that you can address them before bad actors have the chance.
Compliance management
Navigating regulatory requirements is challenging. CSaaS providers help you adhere to industry standards such as GDPR, HIPAA, or PCI DSS, ensuring your business remains compliant and avoids penalties.
Beyond your own internal policies about sensitive information, CSaaS helps to streamline compliance by putting your cybersecurity infrastructure in one place.
Risk assessment
Routine vulnerability assessments and penetration testing are key CSaaS offerings. These proactive measures identify weak spots in your infrastructure and provides actionable steps to strengthen your security posture.
Integrating monitoring, compliance, and risk assessment into your security infrastructure provide critical layers to help keep your data secure. An as-a-service model for your security offers other benefits that help save time and money.
What are the benefits of Cybersecurity as a Service?
There are many benefits to CSaaS you can take advantage of as a business owner. Designed to eliminate risk as part of an automatic, subscription-based model, these benefits include:
- Scalability and flexibility: CSaaS grows with your business. Whether you’re a startup or a multinational company, these services can adapt to meet your evolving security requirements without the need for costly infrastructure upgrades.
- Access to expertise: Building an in-house cybersecurity team can be time-intensive. With CSaaS, your organization benefits from a team of highly skilled professionals specializing in cutting-edge technologies and Zero Trust strategies.
- Cost-effectiveness: Investing in cybersecurity infrastructure and personnel can strain budgets. CSaaS offers predictable subscription-based pricing, making advanced security solutions accessible to businesses of all sizes.
CSaaS enables you to focus on innovation for your core business. Also, data breaches can hurt your business. CSaaS lets you tap consultants with various regulatory and specific skills, such as threat hunting, incident response, network security, and so on.

AT&T Consulting and Professional Services
Provides advisory and digital transformation services that solve business challenges with technology solutions.
In-House vs. CSaaS: Making the right choice
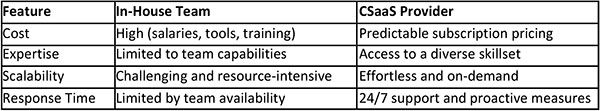
Choosing between an in-house cybersecurity team and outsourcing to a CSaaS provider depends on several factors, including budget, expertise, and scalability needs. While taking ownership of your own team may seem like an attractive option for proactive business owners, CSaaS comes with distinct advantages that can be applied more rapidly for a lower upfront cost.
When you’re in charge of an organization, it feels good to know that data, personal information, and proprietary company details are kept secure.
Outsourcing that task to a CSaaS provider can give you back time and resources you can apply toward growing your business instead of monitoring your network—regardless of your industry or field.
Tailored solutions for every industry
Different sectors face unique cybersecurity challenges. CSaaS adapts to meet these specific needs, providing targeted solutions for the individual needs each industry can present. In financial services, for example, protecting customer data and transactions is paramount to meeting industry regulations.
Patient records in healthcare businesses need to be kept secure to comply with HIPAA. eCommerce platforms for retail businesses must remain protected from credit card fraud and phishing. And manufacturing plants have to shield intellectual property from corporate espionage and ransomware attacks.
In short, businesses of every kind benefit from reliable security that covers more than a basic employee training on data compliance. CSaaS offers a comprehensive solution that is put in place across every avenue of your business.
Use case 1: How CSaaS might work with SASE
A major reason that businesses are utilizing an MSSP for SASE is because it can be difficult and expensive to hire and retain technicians with the specialized skillset that’s needed, particularly if they require 24x7 monitoring.
Another consideration is that while some technology providers claim to offer a complete SASE portfolio, implementing SASE is complex. This makes it even more important to choose a provider that can offer you expert, reliable guidance for your cybersecurity needs.
One of the most important reasons to consider CSaaS is that SASE is not a “one and done” or plug-and-play solution. It’s not feasible to rip out and replace an infrastructure overnight. Most large or well-established companies will be in a hybrid environment for the foreseeable future.
Having assets hosted both on-premises as well as in the cloud requires the expertise a skills-rich CSaaS vendor can provide.
Use case 2: How CSaaS might work with Zero Trust
Zero Trust provides a different lens for data and network security. Some systems have a reliance on old and easily neglected least privilege/whitelisting models. Zero Trust models aim to eliminate trust from every communication packet on the network, whether it originated from inside the organization or outside, and look to gain confidence that the packet is legitimate.
In short, rather than the traditional “trust but verify” approach, it never trusts and always verifies all traffic.
- Zero Trust is built on core tenets: all network flows are authenticated before processing, and access is determined by dynamic policy.
- All transaction flows are cataloged to enforce access.
- Security (authentication and encryption) is applied to all communications independent of location and must be performed at the application layer closest to the asset in the network.
- Comprehensive vulnerability and patch management procedures must be followed.
- Technology is utilized for automation in support of user/asset access and other policy decisions. A Zero Trust architecture requires automation, especially in support of dynamic policy, authorization, and authentication.
- All traffic is controlled and monitored as access is provided.
Given all of this, you can see that having an experienced third party making these recommendations may work better than doing battle with “we’ve always done it that way” beliefs in your organization.
Reputable CSaaS vendors have experience in both working collaboratively with management on the approach and successfully implementing Zero Trust.
How to choose a CSaaS company
When choosing a CSaaS vendor, look at factors such as:
- Technical expertise and depth the MSSP will provide.
- Do they just provide penetration testing and call it a day? As we’ve discussed, that’s not the whole story by a longshot.
- Reputation of the CSaaS vendor. Do they have customers similar to your business? Do they have experience in your industry? Are they financially stable?
- Size of the CSaaS. Can they scale with your business needs as you grow?
- Terms and conditions of the relationship. Details matter. Definitely read the small print to understand all the details in various scenarios. Understand their policies and procedures.
- Cost and fee structure.
- What kind of tools do they use? Make sure their technology is solid.
- Can they support your business 24x7? If you’re in multiple time zones, can they cover you?
- Can they meet the regulatory compliance that you need in your industry?
Protect your business today
AT&T Cybersecurity Services has a large consulting group available for your CSaaS needs. Our cybersecurity consulting team will help you make sure you understand SASE and Zero Trust, as well as how to apply them to your business.
They’ll focus on understanding your business so they can provide the best recommendations for where your business is today to where you plan to grow.
We also want to help you make sure you have the best foundation for your cybersecurity and technology infrastructure. Your network is that foundation and our network consulting services provide you with the guidance you need for network modernization.
Learn more about AT&T Cybersecurity and how our expertise can help. To connect with an expert who knows business, connect with your AT&T Business representative.
Why AT&T Business
See how ultra-fast, reliable fiber, protected by built-in security, and 5G connectivity give you a new level of confidence in the possibilities of your network. Let our experts work with you to solve your challenges and accelerate outcomes. Your business deserves the AT&T Business difference—a new standard for networking.
Updated on March 18, 2026 by Zoya Cochran




Share
Share this with others